Services

Blocking Blacklisting
Blocking and blacklisting are two different methods used to prevent access to certain websites
Preventing Data & Credential Leakage
Data and credential leakage can be a serious problem for businesses, as it can result in data

Malware
Our approach towards Malware protection includes comprehensive services such as:
Use of ant

Fraud
In today's digital world, cyber fraud is becoming an increasingly common threat to businesses.

Threat Hunting
Threat hunting is a proactive approach to cybersecurity that involves searching for and identi

Vulnerability Enrichment
Vulnerability enrichment refers to the process of enhancing or adding additional information t

Risk Management
Risk management is a critical component of cybersecurity. Cybersecurity risk management involv

Dark Web Monitoring
Dark web monitoring is a cybersecurity practice that involves monitoring the dark web for info

Remediation
Remediation in cyber security refers to the process of addressing and mitigating security vuln

Ask The Analyst
CyberCorp is a cybersecurity company that provides a range of products and services designed t

Threat Research Services
Threat research services are an essential aspect of cyber security, as they help organizations
Compliance Assessment
Compliance Assessment in Cyber security refers to the process of evaluating an organization's
Security Advisory Services
Security Advisory Services refer to the professional services offered by Cyber security expert

Threat Third Party
In cyber security, a "third party" refers to any external entity that has access to an organiz
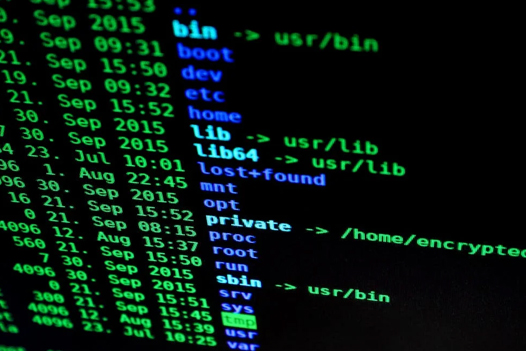
Vulnerability Risk Analyzer
A Vulnerability Risk Analyzer is a tool used in cyber security to identify potential vulnerabi

Threat Intelligence Platform (TIP)
A Threat Intelligence Platform (TIP) is a Cyber security solution designed to provide organiza
Threat Command
Threat Command is a term used in cybersecurity to refer to the process of detecting, analyzing
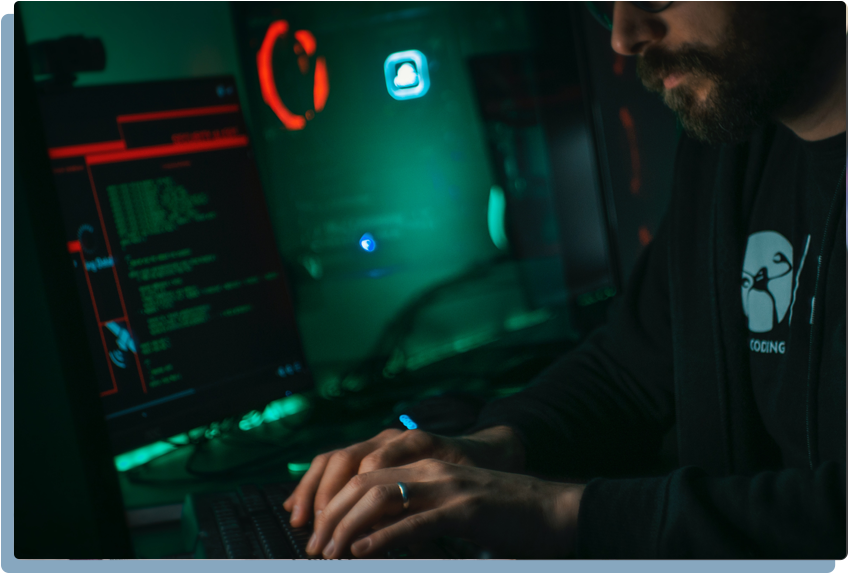
Why CyberCorp is not a mere SPAC?
We are

CoOperative Corporate
Creates a commonwealth among the partners
Cumulative Growth safeguards against losses to one entity
We believe in

Organic Growth
Promotes growth within the group companies
Ensures Maximum benefits
We do

Integration
Horizontal integration of the various products
Creating new and more effective scalable solutions
© 2022-2026 CyberCorp Limited. All Rights Reserved.